Part of the Kubernetes security is to use RBAC for the authentication and authorization. There’s plenty of short articles about that, but I didn’t find any good and complete “how to”-instructions. I hope this will be such. If you want me to clarify something, add it to the comments please. This is done from the Azure AKS point of view when it is integrated with AAD. But many things are the same in other clusters also.
Here’s the description what kind of parts the Kubernetes role and role binding has: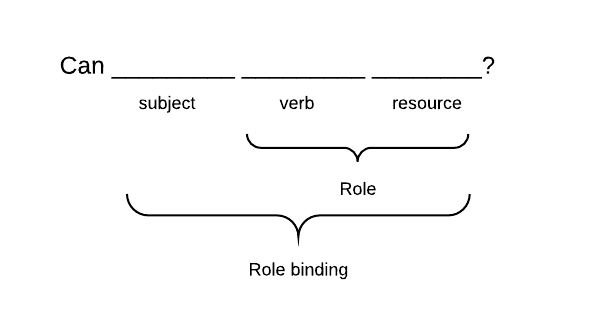
In this terminology “Role” is describing what the binded identity can do. The identity can be a user, group or service account. Roles can be binded to multiple identities. Let’s start to look at the things backwards and start from the Role binding.
kind: RoleBinding
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: <name for the binding>
subjects:
- kind: Group
name: <AAD group ID>
roleRef:
kind: Role
name: <name of the role>
apiGroup: rbac.authorization.k8s.io
Role binding is describing what identity can use the role. For humans the identity is group or single user. The service account is for those pods which have to access the apiserver. User is a single user (like testuser_1@youaaddomain.onmicrosoft.com). The role binding to the single user is useful only if you have a few (less than two) users. With more than one user it will become complex and time consuming to maintain. At AKS AAD integration the Group is the object ID of the AD group. E.g. 6ec5b8f7-823c-491c-97d6-977ae68afbf3.
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
namespace: <mandatory for Role>
name: <name of the role>
rules:
- apiGroups:
- ""
- <some other API group>
resources:
- <resource>
- <another resource>
verbs:
- <verb 1>
- <verb 2>
- apiGroups: # Another block - there can be any number of objects
- <some other API group>
resources:
- <resource>
- <another resource>
verbs:
- <verb 1>
- <verb 2>
The verbs are actions which are allowed. The resources has the following verbs: Create, Get, List, Watch, Update, Patch, Delete, Deletecollection. Addition to those there are several special verbs:
- use verb for the podsecuritypolicies in the policy API group
- bind and escalate verbs on roles and clusterroles resources in the rbac.authorization.k8s.io API group
- impersonate verb on user
You have to read
API documentation what each verb exactly does for each resource.
API Group is the group where the resource belongs to. If the resource is a member of the API group, it must be mentioned in the apiGroups part. The empty string is core. All others must be mentioned. When the resource is searched, the Kubernetes checks all API groups which have been defined for this access right object. If you have defined ‘*’ resource for the access rights, it means that any resource from the defined API groups match with this access.
The resources are divided into two separate groups: Namespace resources and cluster resources. For example, a pod is a namespace resource while a node is a cluster resource. The ClusterRoleis only object which can allow access to the cluster resource. ClusterResource can also allow access to namespace resources. In that case the access is to the resource in all namespaces. The resource binding is done with the ClusterResourceBinding.
If the namespace resources are meant to give access to the specific namespace, the Role is used. The Role defines what namespace is in use. The binding is done with the RoleBinding.